Part 3 : a slice of theory and logical
Let’s move on to the logical side now. But you can still read the previous articles :
- Why you should use GPG ?
- Part 1 : Is there any other way than using GPG ?
- Part 2 : Softwares installation
- Part 3 : a slice of theory and logical
- Part 4 : Create and export your keys
- Part 5 : Sign your mail
- Part 6 : Read and write encrypted mail
- Part 7 : Sign keys
- Part 8 : Sign files
- Part 9 : Encrypt files
- Part 10 : GPG Conf’
OpenPGP, how does it work ?
OpenPGP uses asymmetric cryptography, also called public-key cryptography.
When talking about GPG keys, we actually talk about couples of keys : a public, and a private key.
Does it have to be that complicated ?
When you sign a mail, you want to insure your pen pal that it’s truthful. Same as seals in the Middle-Age : the seal’s wax warranted message’s inviolability.
You have to sign your message with something you’re the only one to possess : your private key !
And how do your pen pals would check this message is authentic ? With something that is well-known, available to anyone : checking signatures is done with your public key !
Opposite, when one encrypt (or cipher) a message, one wants to protect it. You are the only one who should be able to read it with something you are the only one to possess : your private key !
But as anyone should be able to send you encrypted mails, the ciphering operation should be done with something available to anyone : your public key !
Be cautious !
A signed mail can be read by anybody online. Just like a random mail actually.
The signature warrant that you are the true sender and that it has not been altered. So a signed mail has more juridical value than a non-signed mail.
Summary
We sign mail with private key. We check signed mail with the sender’s public key.
We encrypt mails with the recipient public key, and they decrypt with their private key.
It’s always the same side of the liaison that uses the same side of the key: you will always (or almost) use your private key, and your pals will always use your public key.
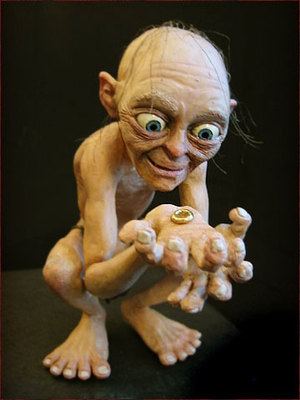
Your private key should be protected like Precious…
It allows you to control your side of the liaison, to prove your identity and read your mail !
Come to read the next article where I tell you how to create the keys.