Second Serie | Part 16 : Going to a gpg signing party
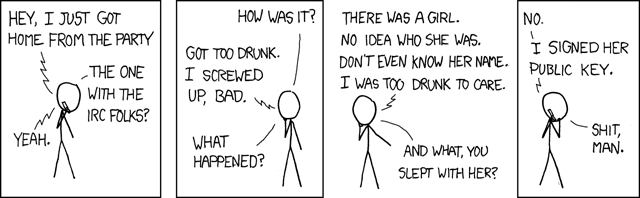
GPG has an important social aspect: it allows people to communicate safely. And it begins in itself by being social: you have to exchange digital ID !
- Part 8 : Sign files
- Part 9 : Encrypt files
- Part 10 : GPG Conf’
- Part 11 : Some details about keys and maths
- Part 12 : Export and import public and private keys
- Part 13 : Various security aspects
- Part 14 : Publish a signing policy
- Part 15 : Using gpg in command line
Going to a gpg signing party
A gpg signing party is an event while a great number of persons will sign each others keys. You gather 50 geeks, and all of sudden, they all exchange key ID and sign each other.
Let’s be serious
Going to a key signing party requires first and foremost good ID proofs. ID cards, passports, driving licence with pictures. Then, of course, papers with mail addresses and key identifiants or fingerprints. Geeks often have their key fingerprint on their business cards. It is not a good idea to use a computer or a phone.
NB : OpenKeyChain software allows to exchange and/or sign easily keys right away. It’s a good thing, but what if you run out of battery ? What if you type something wrong ?
Best way remains to check people’s identity face-to-face, and sign at home.
At a signing party, you may meet a lot of persons with the same motivations : nerds, journalists, researchers, computer enthusiasts, but also simple citizens who wish to protect their privacy. It’s a good way to do networking.
These events enlarge the web of trust, as I described in the article about keys signing. Maybe you will meet there Arthur, and sign his key. Then, later, Georges, who is one of your contacts, will see your signature on Arthur’s key and will use it to contact Arthur.
Non-organized signing party
You meet some persons at a bar, exchange business cards with fingerprints on. OK. Just check each others’ identity and you are good.
The organized signing party …
… or the Zimmermann–Sassaman method is somewhat powerfull.
Those are often organized aside from some larger event, like a free software convention.
- Attendees send a mail to the organizer with the keys enclosed, telling him they intend to come.
- The organizer compile the list of attendees and send it back to the attendees, signed of course.
- Each attendee print the list just before the event, check the organizer’s key and their own in the list.
- At the signing party itself, attendees check that the list is true and accurate.
- When their key is announced, the owner stands to tell it is really their, and everybody can mark the key.
- Then attendees can check each others identity in an ordered manner.
- They can now mark identities as checked.
- At home, they can sign all keys which have the two marks.

This method requires a bit of work for the organizer, but it is really efficient for parties with large groups.
The gigantic signing party …
… or the Zimmermann method in the American way, like a TV show.
Just the same as before, with keys on large screen. Some sort of industrial method to sign half the continent at once.
Back home…
While you are back home, you can actually sign keys.
If you just fetched no more than five or six keys, just sign them and mail.
If you had more keys, it becomes really better to use a script for that, as I told you in the previous article.
Some tools have been created for that. There is for example Caff in the signing party tools (deb package) or pgp-tools on Fedora.
There is also pius which is also lighter, with a Debian package and fedora.
NB : yes, sorry, I only checked those two distrib’s, but I do think it’s easy with the names I gave you to find the softwares on your distrib.
Keybase.io
keybase.io website uses social networks as a proof of identity. If you wish to register, you can ask me, I have some invitations.
You can use their command line client. It is available in ArchLinux communnity repos for example.
But you should definitely avoid sending your private keys on their website.